In the intricate tapestry of global commerce, where opportunities abound and risks lurk in the shadows, two acronyms stand as sentinels guarding the gates of integrity: KYC and AML. Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations are not just bureaucratic hurdles; they are the backbone of ethical business conduct and financial transparency. As businesses navigate the ever-evolving landscape of international markets, understanding these regulations is no longer optional—it’s imperative. This article delves into the essential knowledge every business must possess to not only comply with these critical regulations but to thrive in a world where trust and transparency are the currencies of success. Prepare to embark on a journey that unravels the complexities of KYC and AML, equipping your business with the insights needed to safeguard its reputation and fortify its operations against the unseen threats of financial crime.
Understanding the Core Principles of KYC and AML
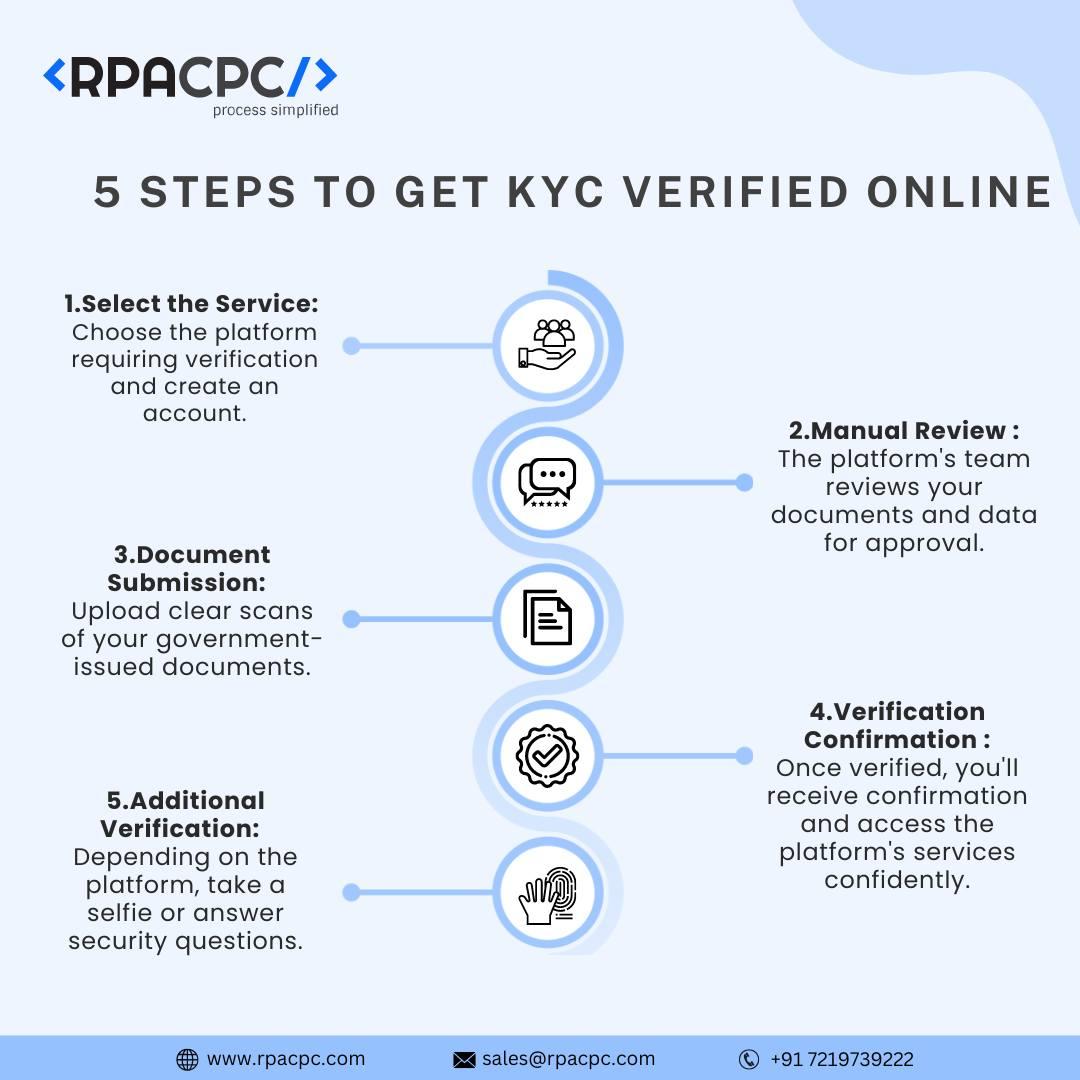
In today’s complex financial landscape, businesses must navigate a myriad of regulations designed to prevent illicit activities. At the heart of these regulations are the principles of Know Your Customer (KYC) and Anti-Money Laundering (AML). KYC is the process of verifying the identity of your clients, ensuring that they are who they claim to be. This involves gathering critical information such as:
- Full legal name
- Address and contact details
- Identification documents like passports or driver’s licenses
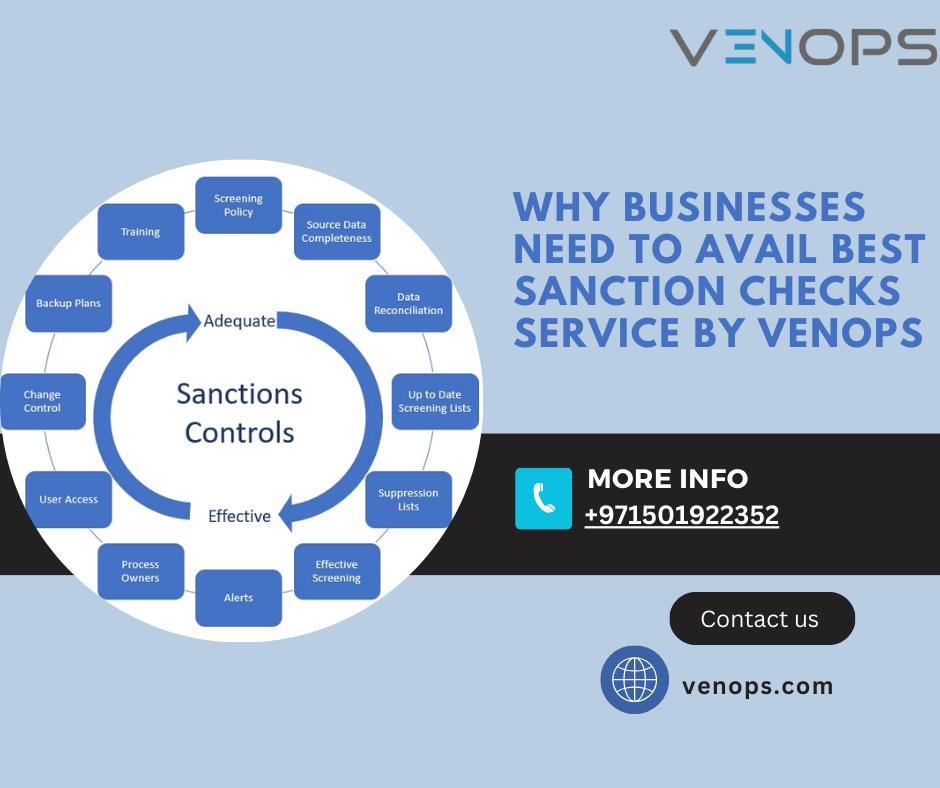
AML, on the other hand, encompasses a broader set of measures aimed at detecting and preventing money laundering activities. This includes:
- Monitoring customer transactions for suspicious activity
- Reporting unusual financial behavior to relevant authorities
- Implementing risk-based approaches to assess potential threats
By integrating these core principles into your business operations, you not only comply with legal requirements but also safeguard your reputation and foster trust with your clientele.
Navigating the Complexities of Regulatory Compliance
In the ever-evolving landscape of business, understanding the intricacies of Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations is crucial for maintaining compliance and safeguarding your organization. These regulations are not merely bureaucratic hurdles but essential frameworks designed to protect businesses from illicit activities and financial crimes. KYC mandates a thorough verification process to confirm the identity of clients, ensuring that your business is not inadvertently facilitating illegal transactions. On the other hand, AML encompasses a broader spectrum of policies aimed at preventing money laundering and terrorist financing, requiring businesses to implement stringent monitoring and reporting mechanisms.
To effectively navigate these regulatory waters, businesses should focus on several key areas:
- Continuous Training: Regularly update your team on the latest regulatory changes and compliance strategies.
- Robust Technology: Invest in advanced software solutions that streamline KYC processes and enhance transaction monitoring.
- Comprehensive Risk Assessment: Conduct periodic evaluations to identify potential vulnerabilities and adjust your compliance strategies accordingly.
- Clear Communication: Establish transparent channels with regulatory bodies to ensure clarity and compliance.
By embedding these practices into your operational framework, you not only mitigate risks but also fortify your business against potential legal and financial repercussions.
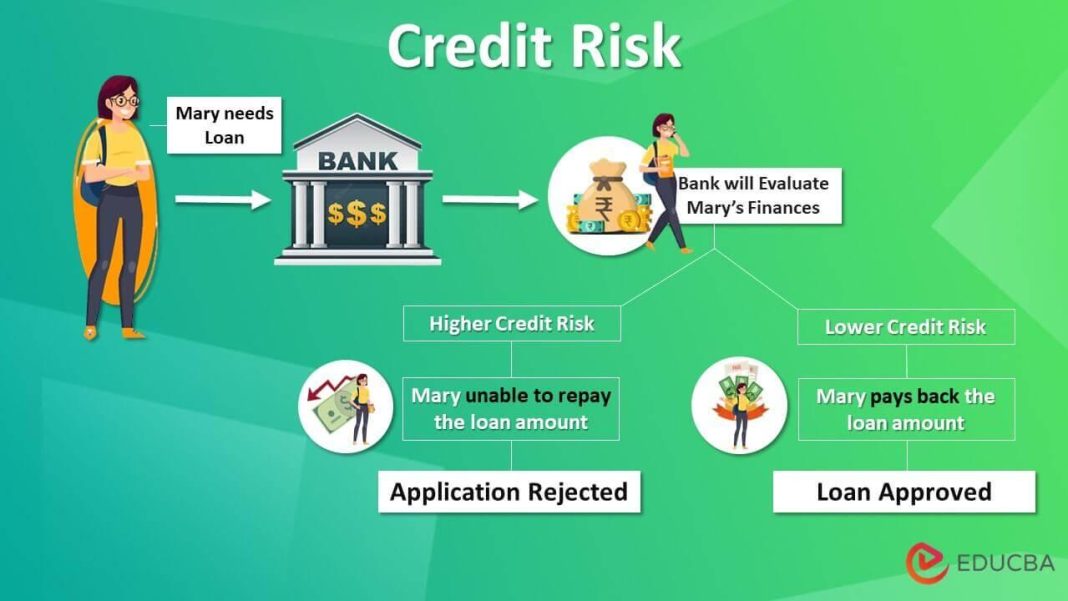
Implementing Effective Strategies for Risk Management
In the ever-evolving landscape of financial regulations, implementing effective strategies to manage risk is paramount for businesses aiming to thrive. A robust risk management framework must incorporate comprehensive Know Your Customer (KYC) and Anti-Money Laundering (AML) protocols. These are not just regulatory requirements but essential components for safeguarding your business against financial crimes and reputational damage.
- Thorough Customer Verification: Establish a multi-layered approach to verify customer identities, using advanced technologies like AI-driven analytics and biometric verification.
- Continuous Monitoring: Implement real-time transaction monitoring systems to detect suspicious activities promptly, ensuring swift action can be taken to mitigate risks.
- Employee Training: Regularly train staff on the latest KYC and AML regulations to ensure they are well-equipped to identify and report potential threats.
- Data Security: Prioritize the protection of customer data with robust cybersecurity measures, minimizing the risk of data breaches and maintaining trust.
By embedding these strategies into your risk management framework, your business not only complies with regulations but also strengthens its defense against financial misconduct, ultimately fostering a secure and trustworthy environment for growth.

Leveraging Technology to Enhance Due Diligence Practices
In the digital age, businesses are increasingly turning to innovative technologies to streamline their due diligence processes, particularly in the realms of Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations. By harnessing the power of artificial intelligence and machine learning, companies can significantly enhance their ability to identify and mitigate risks associated with financial crimes. AI-driven tools can analyze vast amounts of data at lightning speed, flagging suspicious activities that might otherwise go unnoticed. This not only improves the accuracy of risk assessments but also reduces the time and resources traditionally required for manual checks.
- Automated Data Collection: Streamlines the gathering of customer information, ensuring that data is both accurate and up-to-date.
- Real-Time Monitoring: Continuously scans transactions and customer behaviors, providing instant alerts for any anomalies.
- Enhanced Reporting: Generates comprehensive reports that offer deeper insights into potential risks, aiding in more informed decision-making.
Implementing these technologies requires a strategic approach, aligning with regulatory standards while maintaining customer trust. As businesses evolve, so too must their due diligence practices, embracing technological advancements to stay ahead in the fight against financial crime.
Wrapping Up
In the intricate dance of commerce, where opportunity and risk often share the same stage, understanding KYC (Know Your Customer) and AML (Anti-Money Laundering) regulations is not just a matter of compliance—it’s a strategic imperative. As businesses navigate the labyrinthine corridors of global markets, these regulations serve as both a shield and a compass, guiding enterprises towards ethical prosperity while safeguarding against the shadows of illicit activity.
Embracing KYC and AML is akin to mastering a language that speaks to the heart of integrity and trust. It empowers businesses to forge relationships built on transparency and accountability, fostering an environment where innovation can flourish unencumbered by the specter of financial malfeasance. In this ever-evolving landscape, where the only constant is change, staying ahead of regulatory demands is not merely advisable; it is essential.
As we draw the curtain on this exploration, let us carry forward the understanding that KYC and AML are not mere bureaucratic hurdles but vital components of a resilient business strategy. They are the guardians of reputation, the architects of trust, and the custodians of a brighter, more secure commercial future. the businesses that thrive will be those that not only know their customers but also understand the profound responsibility that comes with that knowledge.