In the digital age, where the boundaries of business are defined not by brick and mortar but by bytes and bandwidth, a silent predator lurks, poised to strike at the heart of your enterprise. This predator is not a shadowy figure in a dark alley, but rather a cleverly disguised email sitting innocuously in your inbox. Welcome to the world of phishing attacks—a realm where deception is an art form and your business’s vulnerabilities are the canvas. As cybercriminals become ever more sophisticated, the question is no longer if your business will be targeted, but when. In this article, we delve into the intricate web of phishing threats, exploring the tactics employed by these digital con artists and, more importantly, equipping you with the knowledge to safeguard your business. So, do you truly know how vulnerable your business is to phishing attacks? It’s time to find out.
Understanding the Anatomy of a Phishing Attack
Phishing attacks are not just a simple trickery; they are a sophisticated blend of social engineering and technical deceit. At their core, these attacks are designed to exploit human psychology, leveraging trust and urgency to manipulate individuals into divulging sensitive information. Understanding the anatomy of such an attack is crucial for fortifying your business against these pervasive threats.
Typically, a phishing attack comprises several key components:
- Deceptive Emails: These are crafted to appear as legitimate communications from trusted entities, often mimicking well-known brands or internal departments.
- Malicious Links or Attachments: The email usually contains links leading to counterfeit websites or attachments that, once clicked, install malware on the victim’s device.
- Urgency and Fear Tactics: Attackers often instill a sense of urgency or fear, pressuring the recipient to act quickly without considering the potential risks.
By dissecting these elements, businesses can better prepare and educate their teams, creating a robust defense against the ever-evolving landscape of phishing threats.
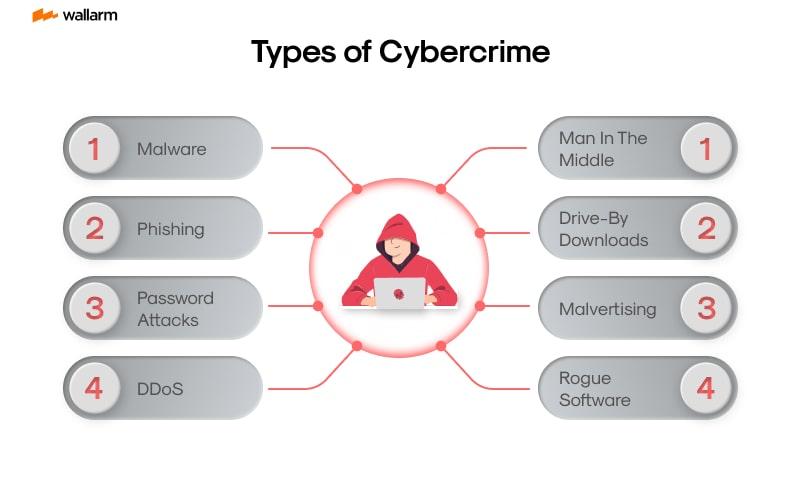
Identifying Red Flags: Common Tactics Used by Cybercriminals
Cybercriminals are becoming increasingly sophisticated, employing a range of tactics designed to deceive even the most vigilant businesses. Recognizing these tactics is crucial in fortifying your defenses against phishing attacks. Here are some common red flags to watch out for:
- Urgency and Fear Tactics: Attackers often create a sense of urgency, prompting hasty actions. Emails claiming your account will be suspended unless immediate action is taken are a classic example.
- Suspicious Sender Information: Phishing emails may appear to come from a legitimate source, but a closer look often reveals discrepancies in the sender’s email address or domain.
- Generic Greetings: Be wary of emails that use generic greetings like ”Dear Customer” instead of your name. Legitimate businesses usually personalize their communications.
- Unusual Attachments or Links: Unexpected attachments or links that direct you to unfamiliar websites are a major red flag. Always verify the source before clicking.
- Poor Grammar and Spelling: Many phishing emails contain noticeable grammatical errors or awkward phrasing, which can be a sign of a scam.
By staying alert to these warning signs, businesses can better protect themselves from falling victim to phishing schemes. Equip your team with the knowledge and tools necessary to spot these threats before they infiltrate your systems.

Strengthening Your Defenses: Essential Security Measures for Businesses
In today’s digital landscape, businesses must be vigilant against the ever-evolving threat of phishing attacks. These cyber threats can infiltrate your organization through seemingly innocuous emails, compromising sensitive data and damaging your reputation. To bolster your defenses, consider implementing the following essential security measures:
- Employee Training: Conduct regular training sessions to educate your team about recognizing phishing attempts. Use real-world examples and simulations to ensure they are well-prepared.
- Advanced Email Filtering: Deploy robust email filtering solutions that can detect and block phishing emails before they reach your employees’ inboxes.
- Multi-Factor Authentication (MFA): Enforce MFA across all business applications to add an extra layer of security, making it more difficult for attackers to gain unauthorized access.
- Regular Security Audits: Schedule frequent security audits to identify vulnerabilities and ensure that your defenses are up-to-date and effective.
By prioritizing these measures, businesses can significantly reduce their risk of falling victim to phishing attacks, safeguarding their assets and maintaining customer trust.

Cultivating a Cyber-Aware Culture: Training and Best Practices for Employees
In today’s digital landscape, the threat of phishing attacks looms large over businesses of all sizes. It’s crucial to empower your employees with the knowledge and skills they need to identify and thwart these malicious attempts. Training programs should be an integral part of your cybersecurity strategy, focusing on real-world scenarios and hands-on exercises. Consider implementing regular workshops and simulations that mimic actual phishing tactics. This not only helps in building awareness but also enhances employees’ ability to respond effectively under pressure.
Beyond training, fostering a culture of vigilance is essential. Encourage open communication where employees feel comfortable reporting suspicious emails without fear of reprimand. Create a checklist of best practices that employees can easily refer to, such as:
- Verifying the sender’s email address before clicking on any links.
- Looking for inconsistencies in email content and language.
- Avoiding the download of attachments from unknown sources.
- Using multi-factor authentication to add an extra layer of security.
By embedding these practices into your organizational culture, you can significantly reduce the risk of falling victim to phishing attacks, safeguarding your business’s valuable data and reputation.