In the intricate dance of global commerce, where borders blur and opportunities abound, the specter of fraud looms as a formidable adversary. As businesses venture into the vast expanse of international markets, the promise of growth is tempered by the peril of deceit. Navigating this complex landscape demands more than just vigilance; it requires a strategic approach rooted in knowledge and foresight. This article serves as your compass, guiding you through the essential strategies to fortify your transactions against the ever-evolving threat of fraud. With an authoritative lens, we delve into the nuanced world of international trade, unraveling the layers of risk and unveiling robust solutions to safeguard your enterprise. Prepare to embark on a journey where security meets opportunity, and where the art of reducing fraud risk becomes an integral part of your global success story.
Understanding the Landscape of International Fraud Risks
In today’s interconnected global economy, businesses face a myriad of challenges when it comes to safeguarding their international transactions. The diverse nature of cross-border dealings introduces unique vulnerabilities that fraudsters are keen to exploit. Recognizing the different types of fraud risks is the first step in fortifying your defenses. These risks can range from identity theft and phishing schemes to more sophisticated threats like trade-based money laundering and invoice fraud. Each type of fraud requires a tailored approach to effectively mitigate its impact.
To navigate this complex landscape, companies must implement robust risk management strategies. Consider the following key practices:
- Enhance due diligence: Conduct thorough background checks on all international partners and clients to ensure their legitimacy.
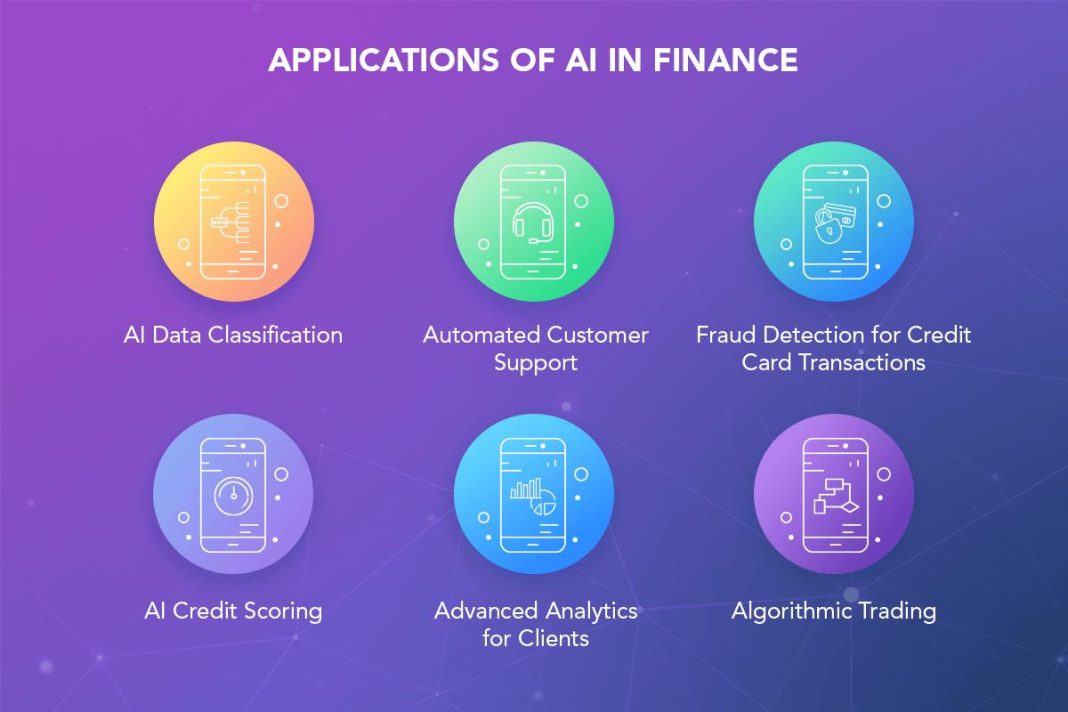
- Leverage technology: Utilize advanced analytics and machine learning tools to detect unusual transaction patterns and anomalies.
- Establish strong internal controls: Implement comprehensive policies and procedures to monitor and manage transaction processes.
- Regular training: Educate employees about the latest fraud tactics and how to recognize red flags.
By adopting these measures, businesses can significantly reduce their exposure to international fraud risks, ensuring smoother and more secure transactions across borders.
Implementing Robust Verification Protocols for Cross-Border Transactions
To effectively mitigate fraud risk in international transactions, businesses must adopt comprehensive verification protocols that are both stringent and adaptable to the complexities of cross-border operations. Utilizing multi-layered authentication methods is crucial, ensuring that each transaction undergoes a series of checks before approval. This can include:
- Two-factor authentication (2FA), which adds an extra layer of security by requiring users to provide two different types of information.
- Biometric verification, leveraging unique physical characteristics like fingerprints or facial recognition to confirm identity.
- Geolocation tracking, which helps verify the legitimacy of a transaction by comparing the location of the transaction with the customer’s usual location patterns.
Moreover, integrating artificial intelligence and machine learning algorithms can enhance the detection of unusual patterns and potential fraud attempts. These technologies can analyze vast amounts of transaction data in real-time, identifying anomalies that human oversight might miss. Additionally, maintaining a robust data encryption protocol ensures that sensitive information is securely transmitted and stored, safeguarding against data breaches and unauthorized access. By implementing these measures, businesses can significantly reduce the risk of fraud in international transactions, ensuring secure and trustworthy cross-border commerce.
Leveraging Technology to Enhance Transaction Security
In today’s digital age, safeguarding international transactions demands a robust technological framework. Advanced encryption protocols play a pivotal role in ensuring data integrity and confidentiality. By employing end-to-end encryption, businesses can secure sensitive information from potential cyber threats. Moreover, multi-factor authentication (MFA) adds an extra layer of security, making it significantly harder for unauthorized users to gain access. Implementing MFA, which often combines something the user knows (like a password) with something they have (such as a smartphone app), is a proven strategy to deter fraudsters.
Additionally, blockchain technology is revolutionizing the way transactions are verified and recorded. Its decentralized nature ensures that each transaction is transparent and immutable, reducing the risk of tampering and fraud. Businesses are also turning to artificial intelligence and machine learning to monitor transactions in real-time. These technologies can identify unusual patterns and flag suspicious activities, enabling swift action to prevent potential fraud. By integrating these cutting-edge technologies, companies can significantly enhance the security of their international transactions, ensuring trust and reliability in the global marketplace.
Developing a Comprehensive Fraud Response Strategy
In the realm of international transactions, the threat of fraud looms large, demanding a robust and multifaceted response strategy. Crafting such a strategy involves a blend of proactive measures and reactive protocols. Start by implementing a rigorous due diligence process for all new partners and clients, ensuring that their credentials and financial history are thoroughly vetted. Utilize advanced analytics and machine learning tools to monitor transaction patterns and flag anomalies that could indicate fraudulent activity. These technologies can help in identifying subtle patterns that human eyes might miss, thereby reducing the risk of undetected fraud.
Additionally, establish a comprehensive incident response plan that includes the following key elements:
- Real-time Monitoring: Employ continuous transaction monitoring systems to detect and respond to suspicious activities instantly.
- Cross-Border Collaboration: Foster relationships with international regulatory bodies and law enforcement agencies to facilitate information sharing and coordinated responses.
- Employee Training: Conduct regular training sessions to educate staff on the latest fraud tactics and prevention techniques.
- Communication Protocols: Develop clear communication channels to ensure swift internal and external communication in the event of a fraud incident.
By integrating these components into your strategy, you not only enhance your defense against fraud but also fortify your organization’s reputation in the global marketplace.