In the digital age, where data is the new currency and connectivity is the lifeblood of modern enterprises, the specter of ransomware and fraud looms larger than ever. As cybercriminals evolve, so too must the defenses of businesses determined to safeguard their operations and reputation. Welcome to a realm where every click could be a potential threat, and every unguarded moment could spell disaster. This article serves as your compass in navigating the treacherous waters of cyber threats, equipping you with the knowledge and strategies necessary to fortify your business against the relentless tide of ransomware and fraud. With an authoritative voice and a creative approach, we delve into the essential steps to protect your enterprise, ensuring that your digital fortress remains unbreachable. Prepare to transform vulnerability into vigilance, and uncertainty into unwavering security.
Fortifying Your Digital Fortress with Robust Cybersecurity Measures
In today’s digital age, businesses face an ever-evolving landscape of cyber threats, making it imperative to implement comprehensive cybersecurity strategies. A multi-layered approach is crucial to safeguarding your business against ransomware and fraud. Start by ensuring your software and systems are consistently updated to protect against vulnerabilities. Employ advanced firewalls and intrusion detection systems to monitor and block unauthorized access. Data encryption is another essential measure, securing sensitive information both in transit and at rest.
- Employee Training: Conduct regular training sessions to educate employees on recognizing phishing attempts and other fraudulent activities.
- Access Controls: Implement strict access controls, ensuring that only authorized personnel have access to critical systems and data.
- Backup Solutions: Regularly back up your data and store it securely offsite to mitigate the impact of potential ransomware attacks.
- Incident Response Plan: Develop a robust incident response plan to swiftly address and contain any breaches, minimizing damage and recovery time.
By adopting these proactive measures, businesses can significantly reduce their risk exposure and fortify their digital fortresses against the growing threat of cybercrime.
Implementing Employee Training to Thwart Ransomware Attacks
To effectively shield your organization from the pervasive threat of ransomware, it’s crucial to focus on the human element within your cybersecurity strategy. Employee training serves as the first line of defense, empowering your workforce with the knowledge and skills to identify and respond to potential threats. This training should encompass a variety of topics, including:
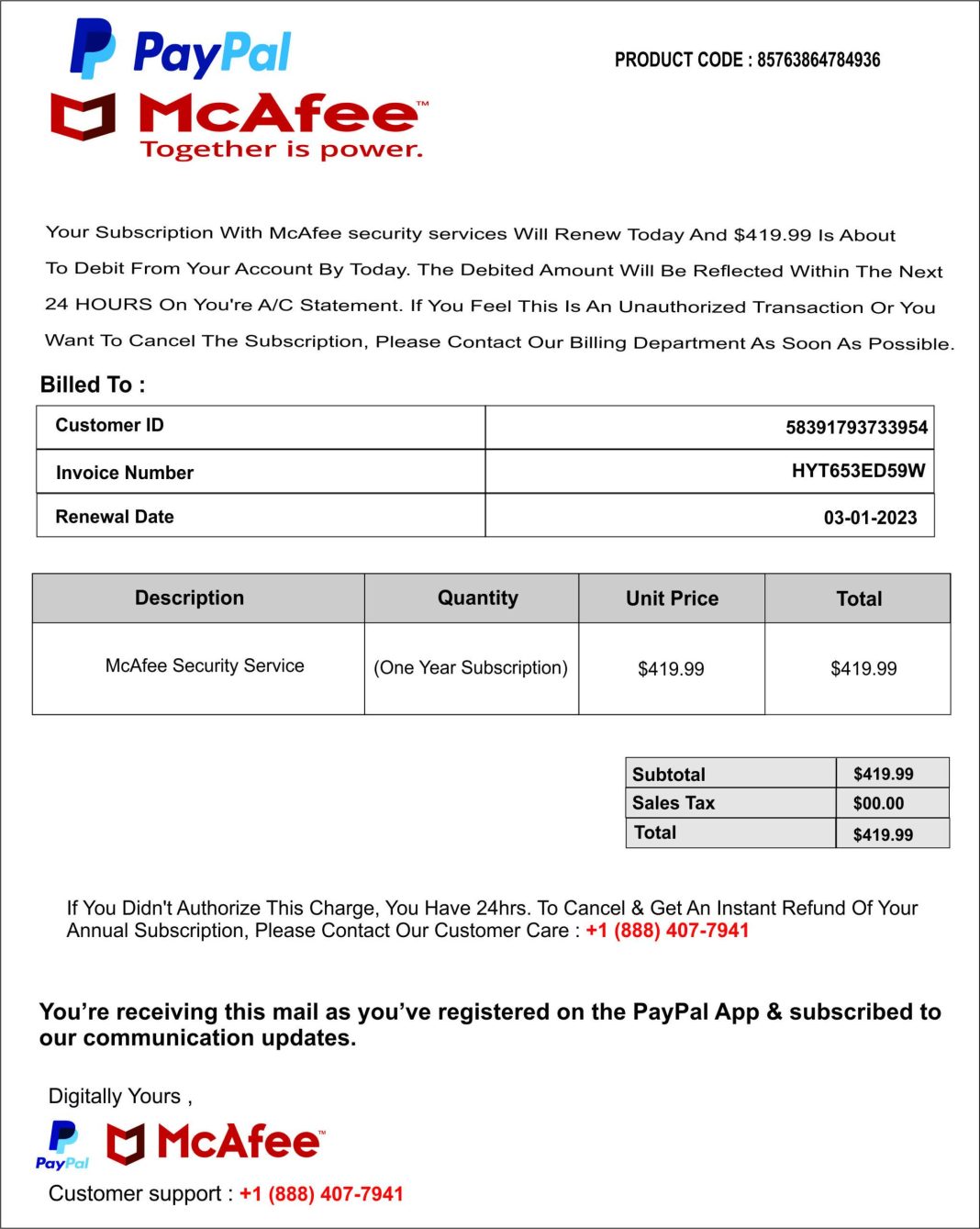
- Recognizing Phishing Attempts: Employees should be adept at spotting suspicious emails and links that could serve as gateways for ransomware.
- Safe Browsing Practices: Educate staff on the importance of avoiding unsecured websites and downloading only from trusted sources.
- Regular Software Updates: Highlight the necessity of keeping software and systems up-to-date to patch vulnerabilities that could be exploited by cybercriminals.
- Data Backup Protocols: Ensure that employees understand the importance of regular data backups and the procedures for doing so, to minimize data loss in the event of an attack.
By instilling a culture of vigilance and preparedness, your business can significantly reduce the risk of falling victim to ransomware attacks. Remember, the strength of your cybersecurity measures is only as robust as the weakest link, often found in untrained personnel. Investing in comprehensive training programs not only fortifies your defenses but also cultivates a proactive mindset among your team members.

Leveraging Advanced Technologies for Fraud Detection and Prevention
In the ever-evolving landscape of cyber threats, businesses must stay one step ahead by embracing cutting-edge technologies designed to combat fraud and ransomware. Artificial Intelligence (AI) and Machine Learning (ML) are at the forefront of this revolution, offering predictive insights and real-time anomaly detection. These technologies can sift through vast amounts of data to identify patterns and irregularities that may signal fraudulent activities, allowing businesses to act swiftly and decisively.
- Blockchain Technology: This decentralized ledger system ensures data integrity and transparency, making it nearly impossible for cybercriminals to alter transaction records.
- Behavioral Analytics: By monitoring user behavior, this technology can detect deviations from normal patterns, flagging potential threats before they escalate.
- Biometric Authentication: Leveraging unique biological traits such as fingerprints or facial recognition, this method provides an additional layer of security that is difficult to replicate.
Implementing these advanced technologies not only fortifies your defenses but also instills confidence among stakeholders and customers, showcasing your commitment to safeguarding sensitive information.
Establishing a Comprehensive Incident Response Plan
In the battle against ransomware and fraud, having a well-defined incident response plan is not just a precaution—it’s a necessity. A robust plan ensures that your business can swiftly and effectively counter any threats, minimizing damage and downtime. Begin by assembling a cross-functional team that includes IT, legal, and communications experts. This team should be well-versed in their roles and responsibilities, ensuring seamless coordination during a crisis. Regular training and simulations are crucial to keep everyone prepared and alert.
Key components of an effective plan include:
- Identification: Quickly detect and assess the nature of the threat.
- Containment: Isolate affected systems to prevent further spread.
- Eradication: Remove the threat completely from your network.
- Recovery: Restore and validate system functionality.
- Lessons Learned: Conduct a post-incident analysis to improve future responses.
Incorporating these elements into your strategy will not only fortify your defenses but also instill confidence among stakeholders, ensuring your business remains resilient in the face of cyber adversities.