In the intricate tapestry of modern business, where transactions weave the fabric of commerce, a silent threat lurks in the shadows: fraudulent billing. Like a master illusionist, fake invoices can seamlessly blend into the backdrop of legitimate paperwork, poised to siphon resources and undermine trust. As businesses grow and transactions multiply, the challenge of discerning genuine from counterfeit becomes ever more critical. This article serves as your compass in navigating these treacherous waters, offering insights and strategies to unmask deceit and safeguard your enterprise. With a keen eye and informed vigilance, you can fortify your defenses against this invisible adversary, ensuring that your financial dealings remain as authentic as the integrity of your business. Welcome to your guide on how to spot fake invoices and prevent fraudulent billing—where knowledge is your most powerful ally.
Identifying Red Flags in Invoice Authenticity
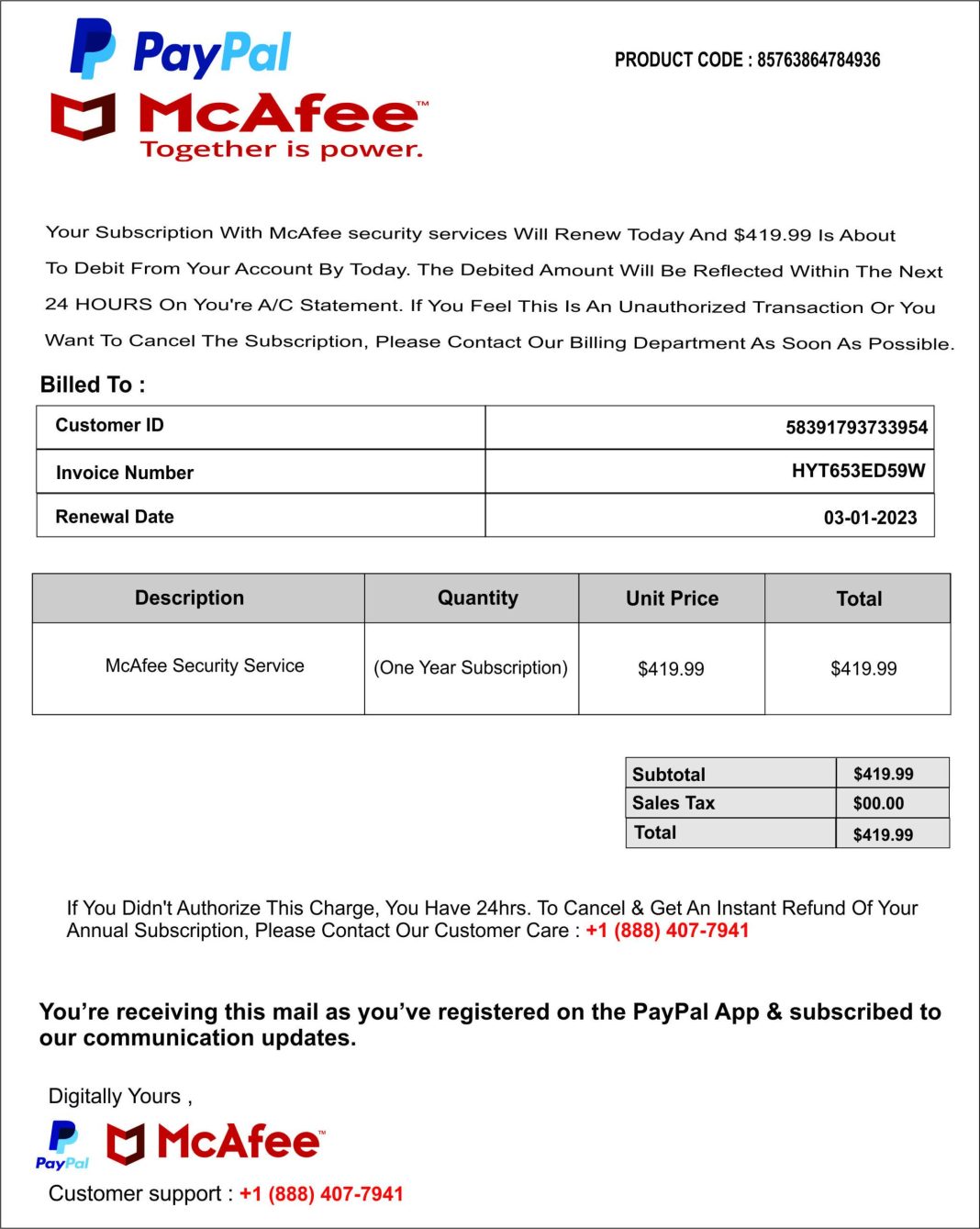
In the fast-paced world of business, distinguishing genuine invoices from fraudulent ones is crucial. Red flags often lurk in the details, and spotting them requires a keen eye. Start by examining the invoice number; inconsistencies or irregular sequences can be telltale signs of forgery. Additionally, scrutinize the vendor details. Mismatched or vague contact information, such as missing phone numbers or generic email addresses, should raise suspicion.
- Unusual Payment Terms: Be wary of invoices demanding immediate payment or offering hefty discounts for quick settlements.
- Inflated Charges: Compare the invoice against previous bills or contracts. Any unexplained increase in rates or quantities should be questioned.
- Spelling and Grammar Errors: Professional invoices are typically free from errors. Multiple mistakes might indicate a lack of authenticity.
By staying vigilant and implementing thorough verification processes, businesses can safeguard themselves against the costly pitfalls of fraudulent billing.
Mastering the Art of Verification Techniques
In the complex world of financial transactions, the ability to discern genuine invoices from fraudulent ones is a crucial skill. The process begins with a keen eye for detail and a systematic approach to verification. Cross-referencing invoice details with purchase orders and delivery receipts is an essential step. Look for discrepancies in item descriptions, quantities, and pricing. Anomalies in these areas often signal fraudulent activity. It’s also wise to scrutinize the vendor’s information; mismatched or unfamiliar vendor details should raise immediate red flags.
- Verify Vendor Authenticity: Ensure the vendor’s contact information matches official records.
- Check Invoice Formatting: Legitimate invoices usually follow a consistent format.
- Monitor Unusual Patterns: Be wary of invoices with sequential numbering or those arriving at odd intervals.
- Use Technology: Implement software solutions that automatically flag inconsistencies and duplicate entries.
Employing these techniques not only safeguards your business from potential losses but also fortifies your financial integrity. By adopting a proactive stance, you ensure that your financial operations remain transparent and secure.
Leveraging Technology to Combat Billing Fraud
In the digital age, technology stands as a formidable ally in the fight against billing fraud. By employing advanced software solutions, businesses can automatically verify the authenticity of invoices, cross-referencing them with purchase orders and delivery receipts. Artificial Intelligence (AI) and Machine Learning (ML) algorithms can detect anomalies and patterns that might indicate fraudulent activities, flagging suspicious invoices for further review. Additionally, blockchain technology offers a transparent and immutable ledger system, ensuring that every transaction is recorded and verifiable.
To effectively utilize technology in combating billing fraud, companies should consider implementing the following strategies:
- Automated Invoice Matching: Integrate systems that automatically match invoices with purchase orders and receipts.
- Real-Time Alerts: Set up real-time notifications for any discrepancies or unusual billing patterns.
- Blockchain Integration: Use blockchain for secure and transparent transaction recording.
- Regular Software Updates: Ensure all fraud detection software is up-to-date to combat the latest threats.
By leveraging these technological tools, businesses can not only detect but also prevent fraudulent billing activities, safeguarding their financial health and maintaining trust with their partners.
Implementing Robust Policies for Invoice Approval
Establishing a solid framework for invoice approval is essential in safeguarding your organization against fraudulent billing. Begin by setting clear guidelines and criteria for invoice validation. Ensure that all invoices are matched against purchase orders and contracts to verify their legitimacy. Implement a multi-level approval process, requiring at least two individuals to review and approve each invoice. This dual-approval system adds an extra layer of scrutiny, reducing the risk of fraudulent invoices slipping through the cracks.
Incorporate technology to streamline and enhance the approval process. Leverage automated tools that can flag discrepancies and anomalies in real-time. Such systems can cross-reference invoice details with existing databases, identifying potential red flags like duplicate invoices or unusual vendor information. Additionally, consider adopting a centralized digital platform for invoice management, which can provide a comprehensive audit trail and facilitate easier monitoring and reporting. By fostering a culture of vigilance and leveraging advanced tools, organizations can effectively combat invoice fraud.