In an era where our lives are increasingly intertwined with the digital realm, the question of identity has taken on a new dimension. As we navigate through this vast digital landscape, the challenge of verifying who we are—and ensuring that others are who they claim to be—has never been more critical. Enter digital identity verification, a powerful tool in the arsenal against fraud. This technology not only safeguards individuals and businesses but also fortifies the very foundation of trust upon which the digital world is built. In this article, we will explore the intricacies of digital identity verification, unveiling its role as a sentinel in the fight against fraud. From understanding its mechanisms to implementing it effectively, we will guide you through the essential steps to harness this technology, ensuring that your digital interactions remain secure and authentic.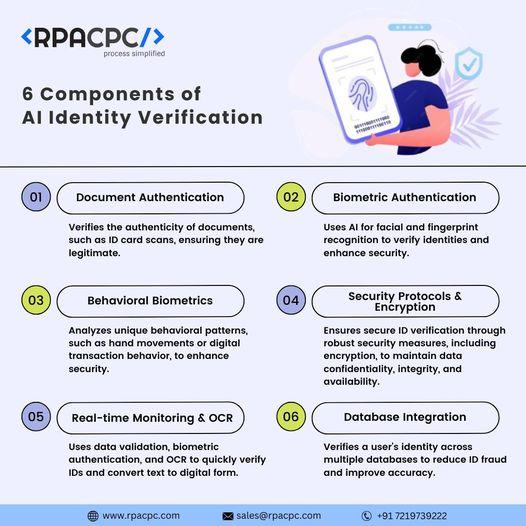
Enhancing Security with Advanced Digital Identity Tools
In today’s digital age, safeguarding personal and organizational data is paramount. Advanced digital identity tools have emerged as a powerful ally in the fight against fraud. By leveraging sophisticated technologies such as biometric authentication, machine learning algorithms, and blockchain, these tools offer robust solutions that ensure only legitimate users gain access to sensitive information.
- Biometric Authentication: Utilize fingerprint, facial recognition, or iris scans to confirm identities with precision.
- Machine Learning Algorithms: Detect anomalies in user behavior to flag potential fraudulent activities in real-time.
- Blockchain Technology: Employ decentralized ledgers to enhance transparency and traceability of identity verification processes.
By integrating these cutting-edge tools into your security framework, you not only enhance the protection of your digital assets but also build trust with your users, ensuring a seamless and secure experience.
Unmasking Fraudsters: Strategies for Effective Identity Verification
In the battle against fraud, the key lies in adopting robust digital identity verification methods. These strategies are designed to unmask fraudsters before they can exploit vulnerabilities. Biometric authentication stands at the forefront, utilizing unique physical traits such as fingerprints or facial recognition to ensure that only legitimate users gain access. Coupled with multi-factor authentication (MFA), which requires multiple forms of verification, this approach significantly reduces the risk of unauthorized access.
- Behavioral Analytics: By analyzing user behavior patterns, such as typing speed or navigation habits, anomalies can be detected that may indicate fraudulent activity.
- Document Verification: Utilizing advanced technologies to verify the authenticity of identity documents, ensuring they are not forged or altered.
- Real-time Data Analysis: Leveraging AI and machine learning to analyze data in real-time, identifying suspicious activities instantly.
Implementing these strategies not only strengthens security but also builds trust with users, assuring them that their identities are protected. By staying ahead of the curve with these innovative solutions, businesses can effectively deter fraudsters and safeguard their digital ecosystems.
Leveraging AI and Machine Learning in Fraud Prevention
In today’s digital landscape, harnessing the power of AI and Machine Learning is essential for robust fraud prevention strategies. These technologies excel in analyzing vast datasets to identify patterns and anomalies that might elude traditional methods. By integrating AI-driven systems, businesses can enhance their digital identity verification processes, ensuring that fraudulent activities are detected and mitigated in real-time.
- Pattern Recognition: Machine learning algorithms can recognize complex patterns and correlations in user behavior, flagging suspicious activities that deviate from the norm.
- Adaptive Learning: AI systems continuously learn and adapt to new fraud tactics, improving their accuracy and efficiency over time.
- Automated Decision-Making: Automated systems can make quick, data-driven decisions to approve or deny transactions, reducing the risk of human error.
By leveraging these advanced technologies, companies not only safeguard their operations but also enhance customer trust and satisfaction. Embracing AI and machine learning is no longer optional—it’s a critical component of a modern, resilient fraud prevention strategy.

Building Trust Through Robust Digital Identity Frameworks
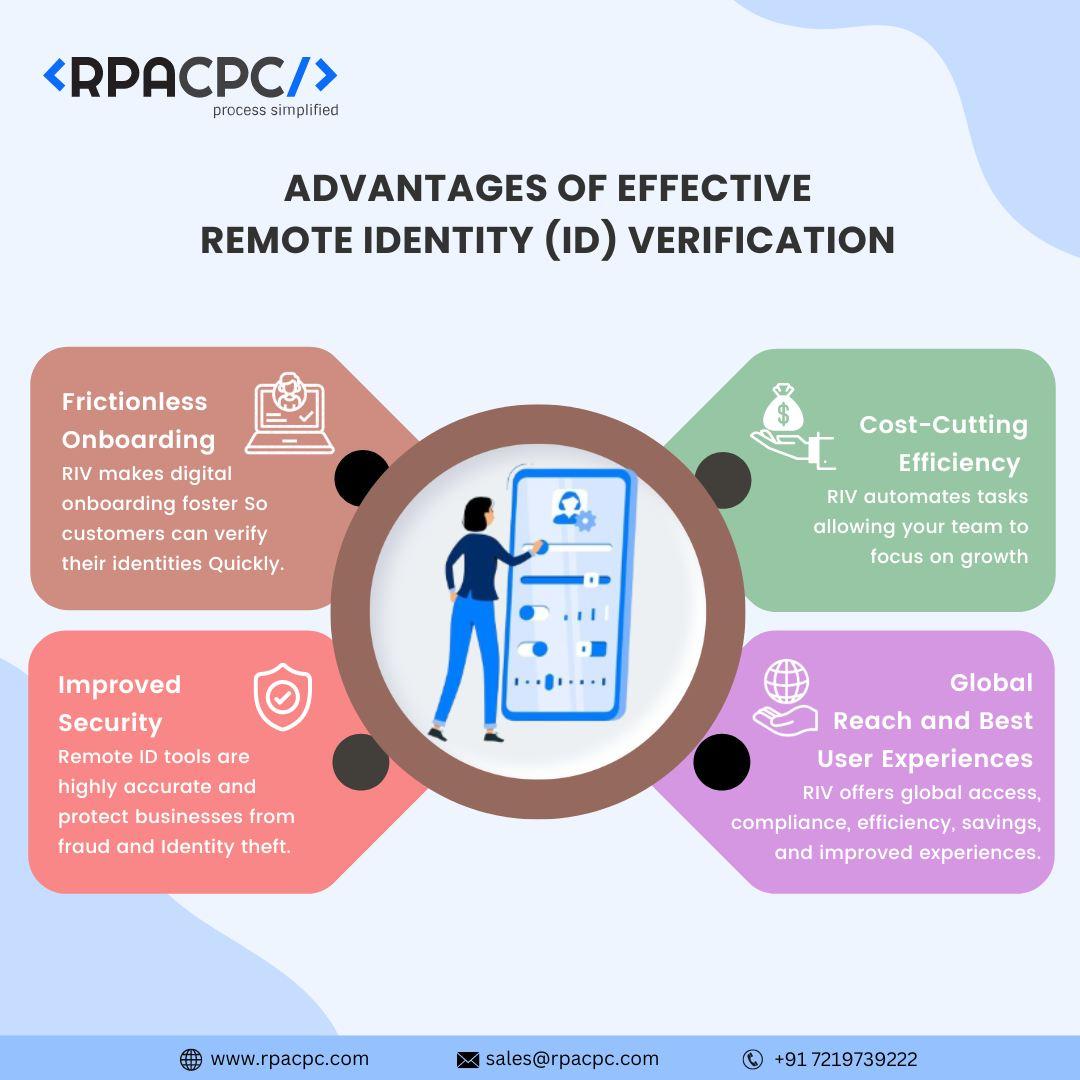
In today’s digital age, ensuring secure and trustworthy interactions is paramount. A robust digital identity framework acts as the backbone for safeguarding online transactions and interactions. By implementing comprehensive verification processes, organizations can significantly reduce the risk of fraud. Digital identity verification involves multiple layers of security measures, including biometric authentication, two-factor authentication, and AI-driven anomaly detection. These measures not only verify the authenticity of the user but also provide a seamless user experience, enhancing trust and reliability.
- Biometric Authentication: Utilizes unique biological traits such as fingerprints or facial recognition to confirm identity.
- Two-Factor Authentication (2FA): Adds an extra layer of security by requiring a second form of verification, often a code sent to a mobile device.
- AI-Driven Anomaly Detection: Leverages artificial intelligence to detect unusual patterns or behaviors that may indicate fraudulent activity.
By integrating these technologies, businesses can not only prevent unauthorized access but also foster a sense of security among their users. This approach not only mitigates risks but also enhances the overall credibility of the digital ecosystem.





