In the digital age, where the click of a button can initiate transactions across continents, the specter of payment fraud looms large, threatening the very foundation of trust in financial systems. As cybercriminals become increasingly sophisticated, the need for robust, cutting-edge technologies to combat these threats has never been more urgent. This article delves into the arsenal of key technologies that are redefining the battlefield against payment fraud. From the silent sentinels of artificial intelligence to the unyielding fortresses of blockchain, we explore how these innovations are not just responding to the evolving tactics of fraudsters but are anticipating and outmaneuvering them. Join us as we navigate the intricate landscape of digital defense, where technology is not just a tool, but a formidable ally in safeguarding the integrity of global commerce.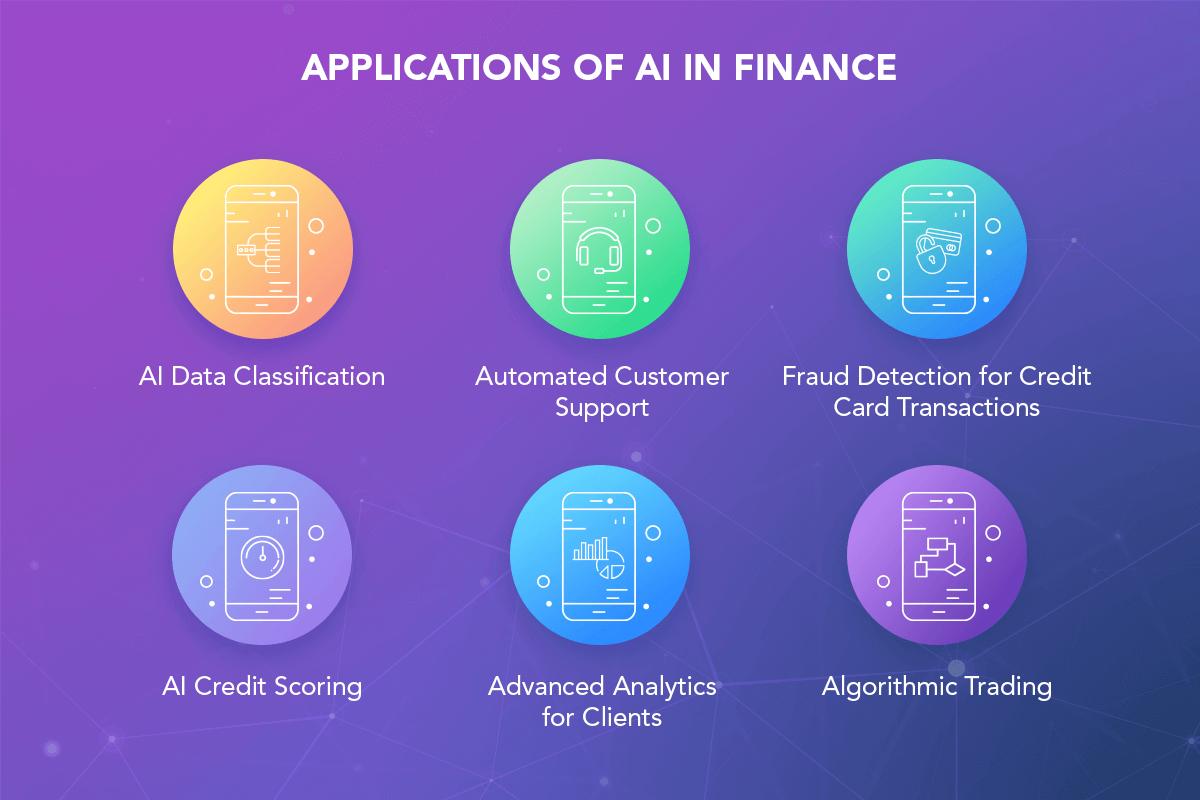
Harnessing Machine Learning for Fraud Detection
In the battle against payment fraud, machine learning emerges as a formidable ally, offering a dynamic and adaptive approach to detecting suspicious activities. By analyzing vast amounts of transaction data, machine learning algorithms can identify patterns and anomalies that might escape traditional rule-based systems. These algorithms continuously learn and evolve, enhancing their accuracy and reducing false positives over time. This adaptability is crucial in an environment where fraudsters are constantly developing new tactics.
- Real-time Analysis: Machine learning models process data in real-time, allowing for immediate detection and response to potential threats.
- Behavioral Biometrics: By understanding user behavior, these models can distinguish between legitimate and fraudulent activities, even if the latter attempts to mimic genuine patterns.
- Anomaly Detection: Sophisticated algorithms can spot deviations from the norm, flagging unusual transactions that warrant further investigation.
With these capabilities, machine learning not only enhances the security framework but also ensures a seamless experience for genuine users, minimizing disruptions while maximizing protection.

Biometric Authentication: A New Era of Security
In the rapidly evolving landscape of digital transactions, biometric authentication stands as a formidable guardian against payment fraud. By leveraging unique physiological traits such as fingerprints, facial recognition, and iris scans, this technology offers a level of security that passwords and PINs simply cannot match. Unlike traditional methods, biometrics are inherently tied to the individual, making them incredibly difficult to replicate or steal. This personal touch not only enhances security but also streamlines the user experience, allowing for seamless and swift transactions.
- Fingerprint Scanning: A widely adopted method due to its accuracy and ease of use, providing a robust barrier against unauthorized access.
- Facial Recognition: Utilizing advanced algorithms to analyze facial features, this method ensures a high level of security while offering convenience.
- Iris Recognition: Known for its precision, this technology scans the unique patterns in the colored part of the eye, offering unparalleled security.
By integrating these cutting-edge technologies, businesses can significantly reduce the risk of fraudulent activities, safeguarding both their assets and their customers’ trust. As we step into this new era, embracing biometric solutions is not just a choice, but a necessity for any organization committed to combating payment fraud effectively.

Blockchains Role in Ensuring Transaction Integrity
In the fight against payment fraud, blockchain technology stands as a formidable ally, providing a robust framework for maintaining the integrity of transactions. At its core, blockchain is a decentralized ledger that records every transaction across a network of computers. This decentralized nature ensures that no single entity has control over the entire chain, significantly reducing the risk of fraudulent activities. By leveraging cryptographic techniques, blockchain ensures that each transaction is securely linked to the previous one, creating an immutable chain of records that is virtually tamper-proof.
Key benefits of blockchain in transaction integrity include:
- Transparency: Every transaction is recorded on a public ledger, allowing participants to verify and audit transactions independently.
- Security: Transactions are encrypted and distributed across the network, making it extremely difficult for hackers to alter or delete information.
- Decentralization: Eliminates the need for intermediaries, reducing the points of failure and potential for fraud.
- Traceability: Provides a clear audit trail, making it easier to track and verify the history of transactions.
By integrating blockchain into payment systems, businesses can enhance trust and reliability, creating a more secure environment for digital transactions.

Real-Time Analytics: The Frontline of Fraud Prevention
In the dynamic world of digital transactions, the ability to analyze data as it flows is nothing short of revolutionary. Real-time analytics empowers businesses to detect and thwart fraudulent activities as they happen, rather than after the fact. This proactive approach relies on several key technologies that work in harmony to scrutinize transactions, identify anomalies, and flag suspicious behavior. By leveraging machine learning algorithms, businesses can continuously learn from new data, refining their detection capabilities and staying one step ahead of fraudsters.
- Machine Learning Models: These models are trained to recognize patterns and anomalies, adapting to new threats as they emerge.
- Behavioral Analytics: By understanding the normal behavior of users, systems can quickly identify deviations that may indicate fraudulent activity.
- Data Visualization Tools: These tools provide intuitive dashboards that allow analysts to see patterns and trends at a glance, making it easier to spot potential fraud.
With these technologies at the forefront, businesses can not only detect fraud in real-time but also predict and prevent it, safeguarding their operations and their customers.