In the rapidly evolving landscape of global commerce, where digital transactions and technological innovations drive unprecedented opportunities, a shadowy underworld of fraud threats emerges with equal vigor. As businesses race to harness the power of new technologies, they must also navigate the treacherous waters of cyber deception and financial subterfuge. This article unveils the top emerging fraud threats that loom on the horizon, poised to challenge the integrity and security of enterprises worldwide. With an authoritative lens, we delve into the sophisticated tactics employed by modern fraudsters, equipping business leaders with the knowledge they need to fortify their defenses and safeguard their hard-earned assets. In this battle of wits, awareness is the first line of defense, and understanding these emerging threats is crucial to staying one step ahead in the relentless game of cat and mouse.
Navigating the Digital Minefield Understanding the Latest Cyber Fraud Tactics
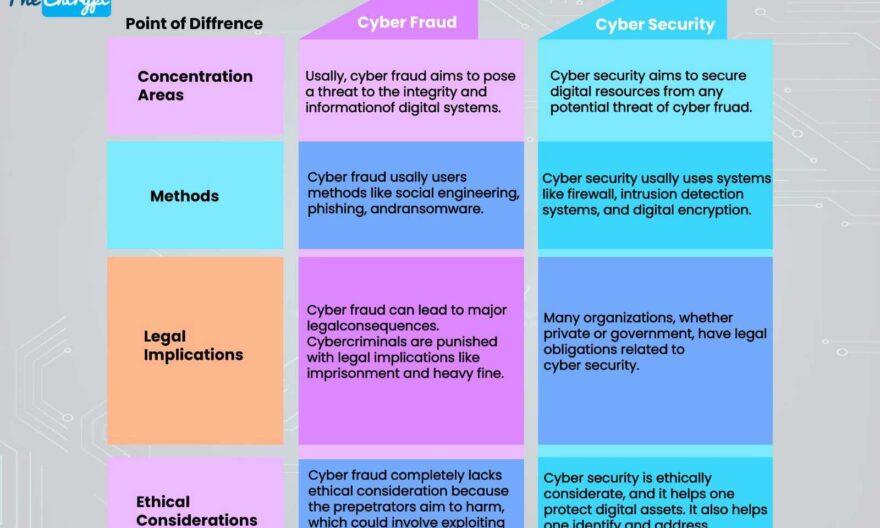
In the ever-evolving landscape of cyber threats, businesses must stay vigilant against the latest tactics employed by fraudsters. These cybercriminals are increasingly sophisticated, leveraging cutting-edge technology to exploit vulnerabilities. Phishing schemes have become more advanced, with attackers using AI to craft highly personalized messages that mimic legitimate communications. Meanwhile, deepfake technology is being harnessed to create convincing audio and video content, making it difficult for businesses to discern fact from fiction.
- Business Email Compromise (BEC): Fraudsters impersonate company executives to trick employees into transferring funds or revealing sensitive information.
- Ransomware-as-a-Service (RaaS): A growing underground market where attackers offer ransomware tools to less skilled criminals, increasing the frequency and variety of attacks.
- Credential Stuffing: Using stolen credentials from one breach to access accounts on multiple platforms, exploiting the common habit of password reuse.
To safeguard against these threats, businesses must invest in robust cybersecurity measures and foster a culture of awareness among employees. Regular training sessions and simulated attacks can help prepare staff to recognize and respond to potential threats effectively.

Inside the Mind of a Fraudster Analyzing Behavioral Patterns and Motives
Understanding the psychological underpinnings of those who commit fraud is crucial for businesses aiming to fortify their defenses. Fraudsters often exhibit a blend of opportunism and calculated risk-taking, driven by motives ranging from financial desperation to the thrill of deception. They meticulously study their targets, identifying vulnerabilities within systems and exploiting them with surgical precision. This calculated approach often involves impersonating trusted figures or manipulating digital environments to create a façade of legitimacy.
Common behavioral patterns include:
- Social Engineering: Leveraging personal information to manipulate individuals into divulging confidential data.
- Phishing Schemes: Crafting emails or messages that mimic legitimate communications to extract sensitive information.
- Insider Threats: Employees or associates exploiting their access to commit fraud from within.
Recognizing these patterns and motives allows businesses to anticipate and mitigate risks, implementing robust security measures that not only protect assets but also deter potential fraudsters from attempting breaches.

Fortifying Your Defenses Essential Strategies for Fraud Prevention
In an era where digital landscapes are continuously evolving, businesses must adopt a proactive stance to shield themselves from the ever-growing specter of fraud. To effectively bolster your defenses, it is crucial to implement a robust strategy that encompasses a variety of essential tactics. Begin by enhancing your cybersecurity infrastructure; this involves regularly updating software and employing advanced encryption techniques to safeguard sensitive data. Additionally, fostering a culture of vigilance among employees is paramount. Equip your team with the knowledge to identify and report suspicious activities, ensuring they remain a critical line of defense.
- Continuous Monitoring: Implement real-time monitoring systems to detect anomalies and unauthorized access swiftly.
- Multi-Factor Authentication (MFA): Require multiple forms of verification to access critical systems, adding an extra layer of security.
- Regular Audits: Conduct frequent audits to identify potential vulnerabilities and ensure compliance with security protocols.
- Vendor Management: Assess and monitor third-party vendors to mitigate risks associated with external partnerships.
By integrating these strategies, businesses can significantly reduce their exposure to fraud, ensuring a more secure and resilient operational environment.
Harnessing Technology The Role of AI and Machine Learning in Detecting Fraud
In the battle against fraud, businesses are increasingly turning to the power of Artificial Intelligence (AI) and Machine Learning (ML)
Key benefits of leveraging AI and ML in fraud detection include: By integrating AI and ML into their fraud prevention strategies, businesses not only enhance their security posture but also build trust with customers, demonstrating a commitment to protecting sensitive information in an increasingly digital world.